这是一篇关于“ATM Skimmers”的文章,摘自:http://krebsonsecurity.com/all-about-skimmers/。
你可能会问什么是“ATM Skimmers”?
ATM Skimmers 直译过来为 ATM 分离器,是一种依附在正常自动提款机上的硬件设备,通常覆盖在键盘、银行卡插槽上,伪装成正常的键盘和银行卡插槽,并且与原设备严丝合缝,基本上普通用户很难区别出来假的键盘、银行卡插槽,用来窃取用户输入的密码以及银行卡数据的一种电子硬件设备。
记录到的密码以及银行卡信息发送的方式也多种多样,有基于GSM通讯模块的发送方式,还有蓝牙发送的,方式很多,我发几张图,你就明白了。





这种玩意儿国外很多,并且很多年前就开始研究了,国外的黑客都喜欢玩硬件,个个精通单片机、电子设计、电路设计,国内我是没见过有,感叹一下,国内与国外的技术差距实在是太大了。
这个在国外很流行,伪装键盘、读卡器,直接获取受害人账号密码,然后复制一张银行卡(或其它方式也可以取款,例如网上银行,POS机消费等):
银行卡使用的磁条储存信息,容量很小,所以可以储存的信息非常有限,只有账号和密码,使用一个读写卡器就可以完成复制,淘宝有卖。
就可以取钱了,网上有大量此类文章教学。
另外,说到POS机,有很多无良商贩,非法记录用户银行卡账号密码,然后非法贩卖这些信息,和ATM黑客手法是完全一样的,这个也非常流行,所以奉劝大家不要去不是非常正规的POS机刷卡,不然,那天你的钱就被洗干净了。
并且在国外,这个已经发展成一个黑色产业链:
“According to Doten, the U.S. Secret Service estimates that annual losses from ATM fraud totaled about $1 billion in 2008, or about $350,000 each day. Card skimming, where the fraudster affixes a bogus card reader on top of the real reader, accounts for more than 80 percent of ATM fraud, Doten said.”
意思大概为:
据美国特勤局估计,在2008年从ATM欺诈的年度亏损总额达10亿美元,或每天约 350,000 美元,其中使用假读卡器覆盖在真正读卡器上欺诈的方法,占所有ATM欺诈的80%。
很恐怖吧,呵呵……
有兴趣的还可以去:
http://krebsonsecurity.com/about/
http://krebsonsecurity.com/about-this-blog/
看看这个博主的资料,以下是部分翻译内容:
Brian Krebs 从 1995 年到 2009 年一直在华盛顿邮报当记者,专门写一些安全相关的文章,已超过1300篇,我在1994年获得了国际研究的乔治梅森大学艺术学士学位,当时我对计算机上没有太大的兴趣,直到2001年,当我的整个家庭网络被中国黑客组织溢出,使我对计算机安全产生了强烈的兴趣。
(哈哈,按时间算,那时候应该是中美撞机事件发生后,2001中美黑客大战,具体参阅:http://baike.baidu.com/view/188847.htm,老实交代,谁干的。。。)
我一直在一个旧的惠普电脑上,瞎搞一个默认安装的Red Hat Linux(6.2)操作系统,因为某种原因,我在教自己如何打开备用计算机之中一个强大的防火墙[啊,真讽刺]。也就是说,直到狮子蠕虫(Lion Worm)来袭的时候,我的系统被锁定,两次。
在这个事件发生之后,我决定学到尽可能多的计算机及互联网安全知识,并阅读在当时我手头能得到的关于这个主题的一切资料,这是一种迷恋,也没有松懈下来。
我现在38岁,与我的妻子珍妮弗生活在弗吉尼亚州北部。每当我不在电脑前,我经常用我的空闲时间阅读、写作、烹饪、研究俄罗斯和弹吉他,我也享受相应的读者,所以请给我写留言,告诉我你关于这个博客的想法。
以下是文章的链接与部分简介内容,每一篇都是独立的文章,可以点进去看看。
The series I’ve written about ATM skimmers, gas pump skimmers and other related fraud devices have become by far the most-read posts on this blog. I put this gallery together to showcase the entire series, and to give others a handy place to reference all of these stories in one place. Click the headline or the image associated with each blurb for the full story.
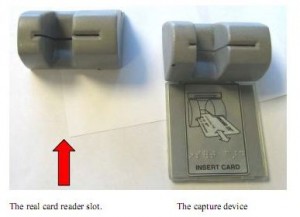
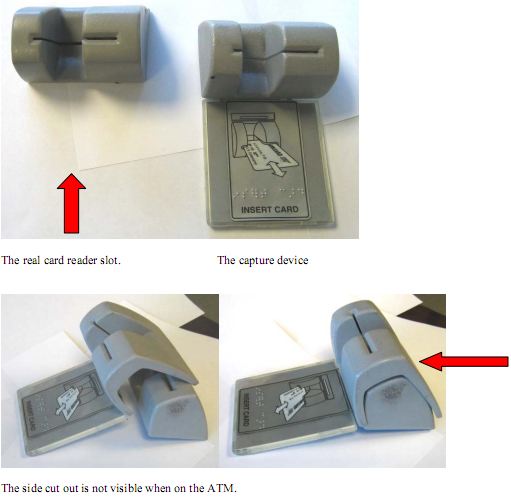
Real card slot on left, skimmer on right.
Jan. 15, 2010: Would You Have Spotted the Fraud? Pictured here is what’s known as a skimmer, or a device made to be affixed to the mouth of an ATM and secretly swipe credit and debit card information when bank customers slip their cards into the machines to pull out money. Skimmers have been around for years, of course, but thieves are constantly improving them, and the device pictured below is a perfect example of that evolution. This particular skimmer was found Dec. 6, 2009, attached to the front of a Citibank ATM in Woodland Hills, Calif. Would you have been able to spot this?
ATM PIN capture overlay device pulled back to reveal the legitimate PIN entry pad.
Feb. 2, 2010: ATM Skimmers, Part II …The U.S. Secret Service estimates that annual losses from ATM fraud totaled about $1 billion in 2008, or about $350,000 each day. Card skimming, where the fraudster affixes a bogus card reader on top of the real reader, accounts for more than 80 percent of ATM fraud. Last week, I had a chance to chat with Rick Doten, chief scientist at Lockheed Martin‘s Center for Cyber Security Innovation. Doten has built an impressive slide deck on ATM fraud attacks, and pictured below are some of the more interesting images he uses in his presentations.
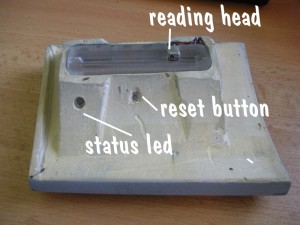
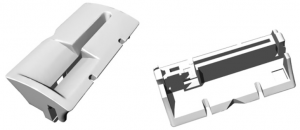
The backside end of a standard, $1,500 Diebold skimmer sold online.
March 25, 2010: Would You Have Spotted This ATM Fraud? …The site also advertises a sort of rent-to-own model for would-be thieves who need seed money to get their ATM-robbing businesses going. “Skim With Our Equipment for 50% of Data Collected,” the site offers. The plan works like this: The noobie ATM thief pays a $1,000 “deposit” and is sent a skimmer and PIN pad overlay, along with a link to some videos that explain how to install, work and remove the skimmer technology.
A bogus PIN pad overlay
June 3, 2010: ATM Skimmers: Separating Cruft from Craft …The truth is that most of these skimmers openly advertised are little more than scams designed to separate clueless crooks from their ill-gotten gains. Start poking around on some of the more exclusive online fraud forums for sellers who have built up a reputation in this business and chances are eventually you will hit upon the real deal.
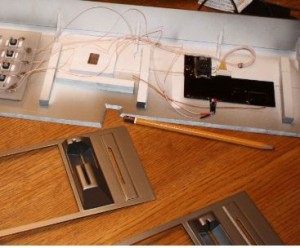
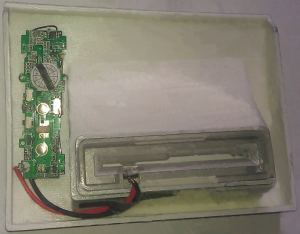
The backside of a GSM-based PIN pad overlay
June 17, 2010: Sophisticated ATM Skimmer Transmits Stolen Data Via Text Message – Operating and planting an ATM skimmer — cleverly disguised technology that thieves attach to cash machines to intercept credit and debit card data — can be a risky venture, because the crooks have to return to the scene of the crime to retrieve their skimmers along with the purloined data. Increasingly, however, criminals are using ATM skimmers that eliminate much of that risk by relaying the information via text message.
Bluetooth-enabled gas pump skimmer.
July 20, 2010: Skimmers Siphoning Card Data at the Pump …Thieves recently attached bank card skimmers to gas pumps at more than 30 service stations along several major highways in and around Denver, Colorado, the latest area to be hit by a scam that allows crooks to siphon credit and debit card account information from motorists filling up their tanks.
Fun With ATM Skimmers, Part III …According to the European ATM Security Team (EAST), a not-for-profit payment security organization, ATM crimes in Europe jumped 149 percent form 2007 to 2008, and most of that increase has been linked to a dramatic increase in ATM skimming attacks. During 2008, a total of 10,302 skimming incidents were reported in Europe. Below is a short video authorities in Germany released recently showing two men caught on camera there installing a skimmer and a pinhole camera panel above to record PINs.
Nov. 10, 2010: All-in-One Skimmers – ATM skimmers come in all shapes and sizes, and most include several components — such as a tiny spy cam hidden in a brochure rack, or fraudulent PIN pad overlay. The problem from the thief’s perspective is that the more components included in the skimmer kit, the greater the chance that he will get busted attaching or removing the devices from ATMs. Thus, the appeal of the all-in-one ATM skimmer: It stores card data using an integrated magnetic stripe reader, and it has a built-in hidden camera designed to record the PIN sequence after an unsuspecting customer slides his bank card into the compromised machine.
Audio skimmer for Diebold ATMs
Nov. 23, 2010: Crooks Rock Audio-based ATM Skimmers – TheEuropean ATM Security Team(EAST) found that 11 of the 16 European nations covered in the report experienced increases in skimming attacks last year. EAST noted that in at least one country, anti-skimming devices have been stolen and converted into skimmers, complete with micro cameras used to steal PINs. EAST said it also discovered that a new type of analogue skimming device — using audio technology — has been reported by five countries, two of them “major ATM deployers” (defined as having more than 40,000 ATMs).
A GSM-based ATM card skimmer.
Dec. 13, 2010: Why GSM-based ATM Skimmers Rule …So, after locating an apparently reliable skimmer seller on an exclusive hacker forum, I chatted him up on instant message and asked for the sales pitch. This GSM skimmer vendor offered a first-hand account of why these cell-phone equipped fraud devices are safer and more efficient than less sophisticated models — that is, for the buyer at least (I have edited his sales pitch only slightly for readability and flow).

Jan. 17, 2011: ATM Skimmers, Up Close…I wasn’t sure whether I could take this person seriously, but his ratings on the forum — in which buyers and sellers leave feedback for each other based on positive or negative experiences from previous transactions — were good enough that I figured he must be one of the few people on this particular forum actually selling ATM skimmers, as opposed to just lurking there to scam fellow scammers.
Jan. 31, 2011: ATM Skimmers That Never Touch the ATM….Media attention to crimes involving ATM skimmers may make consumers more likely to identify compromised cash machines, which involve cleverly disguised theft devices that sometimes appear off-color or out-of-place. Yet, many of today’s skimmer scams can swipe your card details and personal identification number while leaving the ATM itself completely untouched, making them far more difficult to spot.
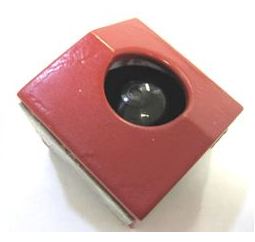
Feb. 16, 2011: Having a Ball With ATM Skimmers …On February 8, 2009, a customer at an ATM at a Bank of America branch in Sun Valley, Calif., spotted something that didn’t look quite right about the machine: A silver, plexiglass device had been attached to the ATM’s card acceptance slot, in a bid to steal card data from unsuspecting ATM users. But the customer and the bank’s employees initially overlooked a secondary fraud device that the unknown thief had left at the scene: A sophisticated, battery operated and motion activated camera designed to record victims entering their personal identification numbers at the ATM.
Mar. 11, 2011: Green Skimmers Skimming Green…To combat an increase in ATM fraud from skimmer devices, cash machine makers have been outfitting ATMs with a variety of anti-skimming technologies. In many cases, these anti-skimming tools take the shape of green or blue semi-transparent plastic casings that protrude from the card acceptance slot to prevent would-be thieves from easily attaching skimmers. But in a surprising number of incidents, skimmer scammers have simply crafted their creations to look exactly like the anti-skimming devices.
April 10, 2001: ATM Skimmers: Hacking the Cash Machine…Most of the ATM skimmers I’ve profiled in this blog are comprised of parts designed to mimic and to fit on top of existing cash machine components, such as card acceptance slots or PIN pads. But sometimes, skimmer thieves find success by swapping out ATM parts with compromised look-alikes.
This paper-thin membrane fits under the real PIN pad.
May 18, 2011: Point-of-Sale Skimmers: Robbed at the Register …Michaels Stores said this month that it had replaced more than 7,200 credit card terminals from store registers nationwide, after discovering that thieves had somehow modified or replaced machines to include point of sale (POS) technology capable of siphoning customer payment card data and PINs. The specific device used by the criminal intruders has not been made public. But many devices and services are sold on the criminal underground to facilitate the surprisingly common fraud.
3D printer firm i.materialise received and promptly declined orders for these skimmer devices.
Sept. 20, 2011: Gang Used 3D Printers for ATM Skimmers …An ATM skimmer gang stole more than $400,000 using skimming devices built with the help of high-tech 3D printers, federal prosecutors say. Apparently, word is spreading in the cybercrime underworld that 3D printers produce flawless skimmer devices with exacting precision. In June, a federal court indicted four men from South Texas (PDF) whom authorities say had reinvested the profits from skimming scams to purchase a 3D printer.
An audio skimmer for a Diebold ATM.
Oct. 13, 2011: ATM Skimmer Powered by MP3 Player …Almost a year ago, I wrote about ATM skimmers made of parts from old MP3 players. Since then, I’ve noticed quite a few more ads for these MP3-powered skimmers in the criminal underground, perhaps because audio skimmers allow fraudsters to sell lucrative service contracts along with their theft devices. The vendor of this skimmer kit advertises “full support after purchase,” and “easy installation (10-15 seconds).” But the catch with this skimmer is that the price tag is misleading. That’s because the audio files recorded by the device are encrypted. The Mp3 files are useless unless you also purchase the skimmer maker’s decryption service, which decodes the audio files into a digital format that can be encoded onto counterfeit ATM cards.
留言评论(旧系统):